On the morning of March 18, 2026, in a Senate Intelligence Committee hearing room, a United States senator asked the FBI director a simple yes-or-no question: Is the FBI still buying Americans’ location data without a warrant?
The answer wasn’t yes or no. It was something more revealing.
“The FBI uses all tools to do our mission,” FBI Director Kash Patel replied. “We do purchase commercially available information that’s consistent with the Constitution and the laws under the Electronic Communications Privacy Act, and it has led to some valuable intelligence for us.”
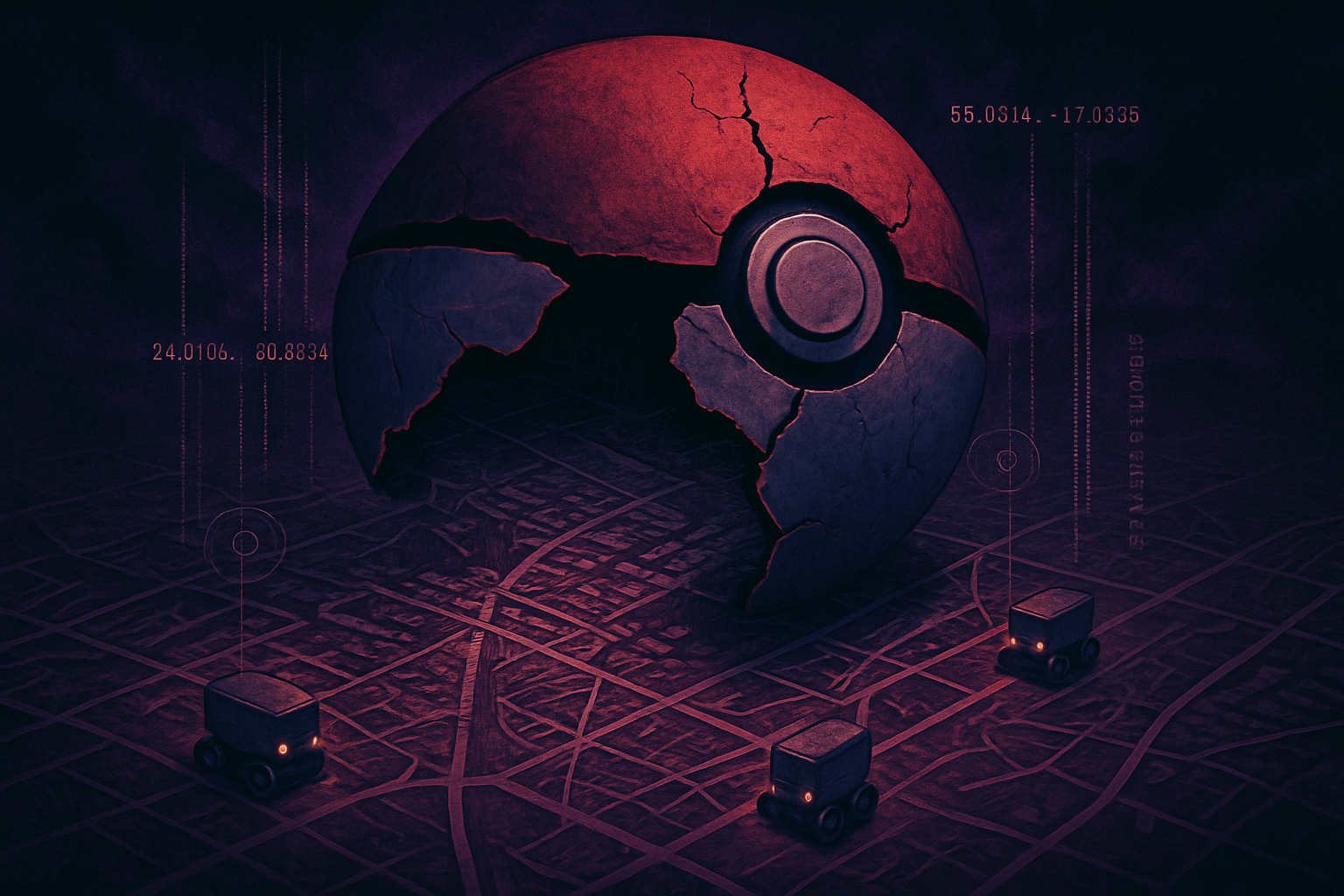
That carefully worded non-denial was a confirmation. The FBI — the most powerful domestic law enforcement agency in the United States — is buying a detailed record of where you go, who you see, and what you do. Not by hacking your phone. Not by getting a judge’s signature. By purchasing data that flows, largely invisibly, from your apps to data brokers to government agencies.
The practice has a name in privacy circles: the data broker loophole. And thanks to a 2018 Supreme Court ruling that didn’t quite go far enough, it is — at least according to the government’s own lawyers — entirely legal.
This is the story of how that loophole works, who’s profiting from it, and what you can do today to make yourself harder to track.
”The FBI Stopped Doing That” — Or Did They?
To understand why the March 18 hearing was significant, you have to go back to 2023.
In a Senate Judiciary Committee hearing three years ago, then-FBI Director Christopher Wray told senators that the Bureau had previously conducted a “specific national security pilot project” that involved buying location data — but claimed the practice was no longer active.
Privacy advocates were skeptical. Senators like Ron Wyden (D-OR) kept asking. Documents kept trickling out. And on March 18, 2026, Wyden finally got his answer — not a denial, but an admission wrapped in bureaucratic language.
“Doing that without a warrant is an outrageous end-run around the 4th Amendment,” Wyden said in response. “It’s particularly dangerous given the use of artificial intelligence to comb through massive amounts of private information.”
Wyden’s frustration carries more than partisan weight. He’s been tracking this issue longer than almost anyone in Washington — it was his office that first publicly revealed in 2021 that the Defense Intelligence Agency had been purchasing, storing, and querying domestic location data collected from Americans’ smartphones. That disclosure came buried in a Senate letter, but the implications were enormous: military intelligence was quietly building databases of American civilian movements, no warrant required.
At the same March 18, 2026 hearing, DIA Director James Adams confirmed the same thing: the DIA continues to purchase “commercially available information.”
Two intelligence agencies. One hearing. Both confirming they buy your location data.
Why This Is — Technically — Legal
Here’s where the law gets both fascinating and infuriating.
The Fourth Amendment to the U.S. Constitution prohibits unreasonable searches and seizures and requires law enforcement to obtain warrants based on probable cause. For most of American legal history, if the government wanted to know where you’d been, it needed a judge’s permission to find out.
Then came the digital age, and with it a legal doctrine that privacy advocates have fought for decades: the third-party doctrine.
The doctrine, derived from 1970s Supreme Court cases like Smith v. Maryland, holds that information you “voluntarily share” with a third party — a phone company, a bank, a credit card company — loses its Fourth Amendment protection. The logic was that by sharing information with someone else, you’ve accepted the risk that they might share it with the government.
For decades, that doctrine let law enforcement access phone records, financial data, and other metadata without warrants. Then, in 2018, the Supreme Court did something remarkable: it pushed back.
Carpenter v. United States: The Case That Changed (But Didn’t Change Enough)
In Carpenter v. United States, Chief Justice John Roberts wrote for a 5-4 majority that the government must obtain a warrant before accessing historical cell-site location information — the time-stamped records generated every time your phone connects to a cell tower.
The opinion was a landmark. Roberts acknowledged that digital technology had fundamentally changed the nature of surveillance: “When the Government tracks the location of a cell phone it achieves near perfect surveillance, as if it had attached an ankle monitor to the phone’s user.” He recognized that even under the third-party doctrine, some records — particularly those that reveal “the whole of a person’s physical movements” — retain a legitimate privacy interest.
Justice Sonia Sotomayor had previewed this reasoning in an earlier case, writing that the third-party doctrine was “ill-suited to the digital age” and shouldn’t apply to information people share with technology companies as a condition of modern life.
Carpenter was a genuine victory. But it contained a critical limitation.
The ruling explicitly applied to wireless carriers — the Verizons and AT&Ts that generate cell-site records directly. The Court explicitly declined to address “what might happen” if the same data was obtained through other means.
Those “other means” are exactly what the FBI is now using.
The Loophole in Plain English
Here’s the Carpenter loophole explained as simply as possible:
The Supreme Court said police need a warrant to get your location from your phone company. But the Court didn’t say anything about buying your location from a company that got it from your weather app.
That’s it. That’s the whole thing.
Wireless carriers have, for years, sold customer location data to data aggregators — a practice the FCC finally sanctioned in 2024 with $196 million in fines against AT&T, Verizon, and T-Mobile. But even as that practice was reined in, a parallel ecosystem had already grown up around a completely different source: mobile apps.
The apps on your phone are, in many cases, location surveillance engines. And the data they collect flows to brokers who sell it to advertisers — and to federal agencies.
The government’s official legal theory? Because this data is “commercially available” to anyone willing to pay, buying it isn’t a “search” under the Fourth Amendment. It’s no different, Senator Tom Cotton (R-AR) argued in the same hearing, than law enforcement searching through someone’s trash left on the curb.
“If any other person can buy it and the FBI can buy it and it helps them locate a depraved child molester or savage cartel leader,” Cotton said in defense of the practice, “I certainly hope the FBI is doing anything they can to keep Americans safe.”
Cotton’s comparison has a certain surface logic. But it ignores scale, permanence, and the nature of what’s actually being bought. A trash can contains discrete items you intentionally discarded. Your location history contains a continuous, granular record of your entire life — where you worship, which doctors you visit, which political rallies you attend, who you sleep next to.
And this legal theory has never been tested in court. No federal judge has ruled on whether the Carpenter warrant requirement extends to broker-purchased location data. The FBI’s position rests on a constitutional interpretation that the Supreme Court’s 2018 opinion left deliberately ambiguous.
The Machine Behind the Surveillance: How Your Data Gets Sold
To understand the FBI’s supply chain, you need to understand how the data broker ecosystem actually works. It’s less a shadowy conspiracy than a mundane industrial process — and you’re the raw material.
Step One: The App Asks for Permission
You download a weather app. Or a navigation app. Or a coupon app. Or a game. The app asks for your location. Sometimes it needs it for the core function — a navigation app that can’t see your location is useless. Sometimes the need is more dubious — why does a flashlight app need to know where you are?
You tap “Allow.” The data starts flowing.
Step Two: The SDK You Never Agreed To
Most apps don’t build their own analytics and advertising infrastructure from scratch. Instead, they embed third-party software development kits (SDKs) — pre-built code packages from advertising and data companies that handle things like ad serving, analytics, and “user engagement.”
Those SDKs often include code that harvests location data and sends it back to the SDK provider — which is frequently a data broker. The app developer gets paid. The broker gets your location. You get… a free app.
A single SDK can appear in hundreds or thousands of apps. One data broker with a popular SDK can, through that single piece of code, receive location data on millions of people simultaneously.
Step Three: Real-Time Bidding — Surveillance by Auction
There’s a second, even more pervasive mechanism: real-time bidding (RTB), the system that runs the mobile advertising economy.
Every time an ad loads in an app, a silent auction happens in milliseconds. Dozens, sometimes hundreds, of advertising companies receive a bid request that includes your location, device identifiers, and behavioral data. Most of them don’t win the auction and don’t show you an ad — but they’ve already received your data.
A 2024 investigation revealed that U.S. Customs and Border Protection had been purchasing data obtained through RTB pipelines — meaning federal agencies were literally tapping into the ad auction infrastructure to collect intelligence on Americans. The data wasn’t being bought from a single broker. It was flowing in from the fundamental plumbing of the mobile advertising economy.
The Scale Is Staggering
A 2025 investigative project called the “Databroker Files” analyzed a single day’s worth of location data and identified 40,000 apps contributing location data to a single broker’s database. One day. One broker. Forty thousand apps.
In 2025, Gravy Analytics — one of the major players in the location data industry — suffered a significant data breach. The breach was a window into just how much sensitive data these companies hold: millions of detailed location histories, cross-referenced with demographic information, stored indefinitely, accessible to paying customers including government agencies.
The Electronic Frontier Foundation has documented that “dozens of data brokers collect information about the precise movements of hundreds of millions of people without their knowledge or meaningful consent” and sell this data to “a variety of private and state actors.”
That last category — state actors — is what we’re talking about.
The Known History of Government Data Purchases
The practice didn’t start with Kash Patel, and it didn’t start with the FBI. Here’s the timeline:
2021 — Senator Wyden publicly reveals that the Defense Intelligence Agency had been purchasing, storing, and querying domestic location data collected from Americans’ smartphones through a chain that ran from app developers through data brokers through defense contractors. The DIA acknowledges the program. The Office of the Director of National Intelligence discloses in writing to Congress that the DIA “does not construe the Carpenter decision to require a judicial warrant endorsing purchase or use of commercially available data for intelligence purposes.” The government’s legal theory, stated baldly, in a congressional letter.
2022–2023 — Ongoing investigations and documents show that Customs and Border Protection (CBP) and Immigration and Customs Enforcement (ICE) were purchasing location data — in ICE’s case, data that was being used to locate and arrest undocumented immigrants in sanctuary cities without getting warrants that local law enforcement would have to honor.
2023 — FBI Director Christopher Wray acknowledges before the Senate Judiciary Committee that the FBI had run a “specific national security pilot project” involving location data purchases, but claims the program is no longer active. Wyden and others remain skeptical.
2024 — Senator Wyden publicly releases documents confirming that the NSA purchases Americans’ internet browsing records — not just location data. The scope of commercially purchased surveillance data extends to what Americans read online. Wyden calls on the Intelligence Community to stop buying data obtained unlawfully from brokers who have violated FTC orders. The FTC takes action against X-Mode Social (now Outlogic), banning the company from selling sensitive location data. The FCC issues $196 million in fines against AT&T, Verizon, T-Mobile, and Sprint for illegally selling customer location data to brokers.
March 18, 2026 — FBI Director Kash Patel and DIA Director James Adams both confirm at a Senate Intelligence Committee hearing that they continue to purchase “commercially available information.” The FBI will not commit to stopping.
What makes 2026 different from 2023 isn’t that the behavior changed. It’s that the admission is now on the record, under oath, in a hearing room, with video. Wray’s claim that the program had stopped was, at best, incomplete.
The AI Amplifier: Why This Got Much Worse
Senator Wyden didn’t just criticize the data purchases in the abstract. He specifically flagged artificial intelligence as a multiplying factor — and he’s right.
Location data, on its own, is revealing but labor-intensive to analyze. A human investigator manually reviewing location history for a single individual has limited capacity to scale. But the era of manually reviewing surveillance data is over.
With AI-powered analytics, bulk location datasets — millions of people, months of history — can be processed automatically. Algorithms can:
-
Identify patterns of association: Who does this person regularly meet? Which devices appear at the same locations? Map social networks without ever touching communications metadata.
-
Infer sensitive activities: Regular visits to a mosque, a Planned Parenthood, an addiction treatment center, a political campaign office, or a domestic violence shelter can be automatically flagged by pattern-matching algorithms.
-
Build “pattern of life” profiles: Not just where you went, but what you do — your routine, your relationships, your deviations. The kind of profile that, before digital technology, would have required sustained physical surveillance by trained agents.
-
Cross-reference across databases: Location data combined with browsing records, purchase history, and social media produces profiles of extraordinary depth. The NSA’s browsing record purchases, combined with location data, create a picture of both where you go and what you think about.
What used to require a team of agents and weeks of work can now be done in seconds, at population scale. The FBI buying location data on millions of Americans doesn’t mean every American is individually investigated — until the algorithm flags you. Then you are.
An Irony Worth Noting
There is a particularly striking irony in Kash Patel’s position.
Patel has been among the loudest critics of what he characterizes as the weaponization of federal agencies against political figures — including, he has alleged, the use of surveillance tools against himself and his allies during the Trump years. He has complained about the FBI accessing phone records and communications without adequate judicial oversight.
And yet, in the same period, he is defending the FBI’s purchase of location data on American civilians without any warrant at all.
The lesson isn’t that one side is right and one is wrong about government surveillance overreach. It’s that surveillance powers, once established, don’t stay pointed only at their original targets. The tools used to track “depraved child molesters and savage cartel leaders” are the same tools that can be turned on journalists, political organizers, religious communities, and government critics. Legal architecture doesn’t come with loyalty oaths.
What Congress Is Trying to Do (And Why It Hasn’t Worked)
The legislative response exists. It’s bipartisan. It’s bicameral. It hasn’t passed.
The Government Surveillance Reform Act (GSRA), introduced by Senators Ron Wyden (D-OR) and Mike Lee (R-UT) in the Senate and Representatives Warren Davidson (R-OH) and Zoe Lofgren (D-CA) in the House, would prohibit federal government agencies from purchasing location data on people in the United States without a warrant or FISA court order. It would extend the same protections to communications content, web browsing history, and internet search history.
This is a genuinely bipartisan effort. Wyden is one of the Senate’s most liberal members. Lee and Davidson are among its most conservative. Lofgren is a senior Democrat. That this coalition exists and has failed to pass the bill is a testament to how entrenched surveillance has become in the national security establishment.
Representative Davidson was direct in his assessment of Patel’s admission: “This is a clear violation of the Fourth Amendment and is why I introduced the Government Surveillance Reform Act — to close the data broker loophole that allows intelligence agencies to buy Americans’ private data.”
The GSRA faces additional urgency because of the upcoming expiration of FISA Section 702 — the surveillance authority that allows collection of foreign intelligence communications — on April 19, 2026. Wyden and his coalition want to use the reauthorization debate to attach the data broker loophole fix to whatever FISA renewal passes. Senator Cotton and supporters of broad surveillance authorities want a “clean” reauthorization with no new privacy restrictions.
That fight is happening right now, and its outcome will determine whether the data broker loophole remains open or begins to close.
What You Can Do: A Practical Defense Guide
You cannot wait for Congress to solve this. The legislative timeline is uncertain; the data sales are happening today. Here’s a concrete, prioritized guide to reducing your exposure.
Priority 1: The App Permission Audit (Highest Impact, Free)
This is the single most effective thing you can do. Most location data flowing to brokers originates as app permissions you granted and forgot about. Rescinding those permissions cuts off the supply at its source.
On iPhone:
- Open Settings → Privacy & Security → Location Services
- Review every app listed. For each one, ask: does this app actually need location to function?
- Change any “Always” permissions to “While Using” or “Never”
- Look especially at: weather apps (use “While Using” at most), coupon and deals apps, games, shopping apps, “free” utilities
Legitimate apps that need location — navigation, transit, find-my-friends — can work with “While Using” rather than “Always.” “Always” means the app can record your location even when you’re not using it, including overnight and in sensitive locations.
On Android:
- Open Settings → Privacy → Permission Manager → Location
- Tap each app to review its permission level
- Change from “Allow all the time” to “Allow only while using” or “Don’t allow”
- Under Settings → Privacy → Ads: tap “Delete advertising ID” — this is critical (see below)
The key question for every app: If I deleted this app right now, what would I lose? If the answer is “nothing important,” delete it. Every app you delete is a source of data you’ve permanently closed.
Priority 2: Kill Your Advertising ID (Critical, Free)
Your advertising ID — called IDFA on iPhone and GAID on Android — is the primary identifier that data brokers use to link your location history across apps and build a persistent profile. Disabling or deleting it makes it dramatically harder to tie your location data to you specifically.
On iPhone (iOS 14.5+):
- Settings → Privacy & Security → Tracking
- Turn “Allow Apps to Request to Track” OFF
- This will prevent new apps from getting your advertising ID. For added protection: Settings → Privacy & Security → Apple Advertising → Personalized Ads → OFF
On Android:
- Settings → Privacy → Ads
- Tap “Delete Advertising ID” (not just opt out — delete it entirely)
- On some Samsung devices: Settings → Privacy → Samsung Privacy → Samsung Ads → disable personalized ads there too
This won’t stop apps from collecting location data entirely, but it significantly degrades the quality of the profiles brokers can build. Without a stable advertising ID, your location pings are much harder to link into a coherent history.
Priority 3: Opt Out of Data Brokers (Tedious, Important)
Your location profile has probably already been assembled and sold. Opting out of data brokers won’t erase historical data that’s already been sold to the government, but it can stop future accumulation and makes your profile less complete going forward.
The reality: There are hundreds of data brokers, and many of them don’t make opt-out easy. But doing the major ones matters.
Start with these high-priority brokers:
- Acxiom (acxiom.com/about-us/privacy/) — one of the largest data compilers
- LexisNexis (lexisnexis.com/privacy/) — used heavily by law enforcement
- Oracle Data Cloud / BlueKai — major ad data aggregator
- LiveRamp (liveramp.com/opt_out/) — identity resolution platform used across advertising
- Lotame (lotame.com/about-lotame/privacy-policy/)
People-finder sites (opt out of all of these): Spokeo, Whitepages, BeenVerified, Intelius, Radaris, PeopleFinder, MyLife — these aggregate personal information and location history into easily-searchable profiles. Search your own name on each and submit removal requests.
Automated removal services (worth considering if you’re serious):
- DeleteMe ($129/year) — handles removal from dozens of brokers and re-scans regularly, since data can re-accumulate
- Incogni (from Surfshark, ~$7/month) — similar automated removal across major brokers
California residents have a powerful option: As of January 1, 2026, California’s DELETE Act created the DROP platform (Data Rights and Opt-Out Platform), a single opt-out mechanism that covers all registered California data brokers. One submission triggers removal requests to the entire registered ecosystem. If you’re a California resident, this is the most efficient path. Visit the California Privacy Protection Agency’s website for the current submission process.
Important caveat: Opt-outs are imperfect. Some brokers don’t fully comply. Data can re-accumulate as you continue using apps. The brokers that sell to government agencies may not be the ones with easy public opt-out pages. Think of opt-outs as raising the cost of tracking you, not eliminating it.
Priority 4: Network-Level Protection (VPN)
A VPN (Virtual Private Network) masks your IP address from the apps and websites you use, making it harder to correlate your activity across different services or link your online behavior to a physical address.
VPNs do not block GPS-level location access — if you’ve given an app location permission, it can still see where you are regardless of VPN use. But a VPN does help in several ways:
- Prevents ad networks from using your IP address as an identifier to link browsing across sites
- Masks your location from services that use IP geolocation (less precise than GPS, but still used)
- Encrypts your traffic from your ISP, which is itself a data broker
Recommended: Look for a VPN with a published no-logs policy, an independent audit, and ideally an open-source client. Avoid free VPNs — they frequently monetize user data, which defeats the purpose.
Priority 5: High-Risk App Categories — Know What You’re Dealing With
Not all apps carry the same risk. These categories are the most likely to be feeding location data into broker ecosystems:
Highest risk:
- Free weather apps — almost universally request location; many monetize this data directly. Use your phone’s built-in weather app (Apple Weather, Google Weather) instead.
- Coupon and retail deals apps (Honey, Ibotta, RetailMeNot, etc.) — location tracking is often core to their business model, not just their features
- “Family tracking” apps — legitimate use case, but data is frequently shared extensively; review privacy policies carefully
- Ad-supported games — RTB infrastructure embedded in mobile games is a major pipeline for location data collection
- News apps with aggressive advertising — RTB in ad-supported news apps exposes your location to dozens of ad bidders per page load
Lower risk (but still audit):
- Navigation apps — need location to function, but use “While Using” not “Always”
- Food delivery apps — need location for delivery, but review post-order permissions
Priority 6: Longer-Term Privacy Practices
These changes compound over time and reduce the overall data footprint that brokers can build on you:
Communication: Use Signal for sensitive messaging. End-to-end encrypted, no metadata sold, no location data harvested. The gold standard.
Browsing: Use Brave or Firefox with the uBlock Origin extension. Both block the RTB tracking infrastructure that’s embedded across the web and in mobile browsers. In-app browsers (when you click a link inside Facebook or Instagram) are significantly harder to protect — avoid them when possible.
Payments: Cash for sensitive purchases. Credit and debit card transaction data is also sold to data brokers, and purchase patterns can reveal medical conditions, political affiliations, and religious practices.
Email: A privacy-focused email provider like Proton Mail reduces cross-site identity linkage, since your email address is often the identifier used to tie your data across different broker databases.
Wireless connectivity: Turn off Wi-Fi and Bluetooth when you’re not actively using them, particularly in commercial spaces. Retail stores and shopping centers use Wi-Fi probe requests (your phone automatically searching for known networks) and Bluetooth signals to track movement through physical spaces — separate from GPS tracking entirely.
The Bigger Picture
What Kash Patel confirmed on March 18 isn’t a scandal in the traditional sense. No law was obviously broken. No court has ruled the practice unconstitutional. The data market that fed the FBI its location profiles operates mostly in the open — publicly traded companies, FTC-regulated (if poorly) entities, venture-backed startups.
What’s happening is more systemic, and in some ways more troubling: the architecture of commercial surveillance and the architecture of government surveillance have become the same architecture. The apps, the SDKs, the RTB auctions, the data brokers — they were built for advertising. But they function, seamlessly, as a warrantless surveillance network.
The Carpenter decision was a genuine step forward. But Roberts wrote the opinion narrowly — deliberately leaving room for future cases to address different technologies and different data flows. Those future cases haven’t come yet. The government’s practice of buying what it can’t subpoena has been operating in that gap for years, and it’s accelerating.
The Government Surveillance Reform Act would close this loophole legislatively without waiting for the courts. Whether it passes will depend on whether enough members of Congress decide that “commercially available” doesn’t mean “constitutionally available” — that the Fourth Amendment’s protection of “the whole of a person’s physical movements” doesn’t vanish the moment that data passes through an app and a broker before reaching a federal agency.
Until there’s a legislative fix or a definitive court ruling, the only reliable protection is making your location data harder to collect in the first place.
The FBI isn’t hacking your phone. It’s buying a detailed profile of your life — assembled, without your meaningful knowledge or consent, from the dozens of apps you use every day. The law hasn’t caught up to the technology. Until it does, the most effective thing you can do is make yourself a less valuable product.
Revoke the permissions. Kill the advertising ID. Opt out where you can. Use apps that respect your privacy instead of monetizing it.
Your location history is yours. The current legal framework says the government can buy it. But it can only buy what exists — and you can limit what exists.
Quick Reference: Privacy Action Checklist
Do today:
- Audit ALL app location permissions (iOS: Settings → Privacy → Location; Android: Settings → Privacy → Permission Manager)
- Change all “Always” location permissions to “While Using” or “Never”
- Delete advertising ID (Android: Settings → Privacy → Ads → Delete Advertising ID)
- Disable app tracking on iPhone (Settings → Privacy → Tracking → off)
- Delete apps you don’t actively use
Do this week:
- Submit opt-out requests to Acxiom, LexisNexis, LiveRamp, Oracle Data Cloud
- Opt out of people-finder sites: Spokeo, Whitepages, BeenVerified, Intelius
- California residents: submit DROP platform request (California Privacy Protection Agency)
- Install uBlock Origin in your browser (Firefox or Brave)
Consider longer-term:
- Subscribe to DeleteMe or Incogni for automated broker removal
- Switch to Signal for sensitive messaging
- Use a reputable VPN
- Switch to Brave or Firefox as default mobile browser
- Replace free weather apps with your phone’s built-in option
Resources and Further Reading
- Government Surveillance Reform Act (2026): Legislation to close the data broker loophole — contact your senators and representative to support it
- Electronic Frontier Foundation (eff.org): Ongoing coverage of location data brokers and government surveillance
- California Privacy Protection Agency (cppa.ca.gov): DROP platform for California residents
- Privacy Rights Clearinghouse (privacyrights.org): Data broker opt-out guides
- Brennan Center for Justice: Research on the third-party doctrine and digital surveillance
- EPIC (epic.org): Analysis of ODNI reports on intelligence agency data purchases
- Senate Intelligence Committee hearing, March 18, 2026: Primary source for Patel’s admission (YouTube, timestamp ~1:11:42)
This article was published on myprivacy.blog. The legal analysis in this piece reflects publicly available information and published legal scholarship. Nothing here constitutes legal advice.